Docs - Team
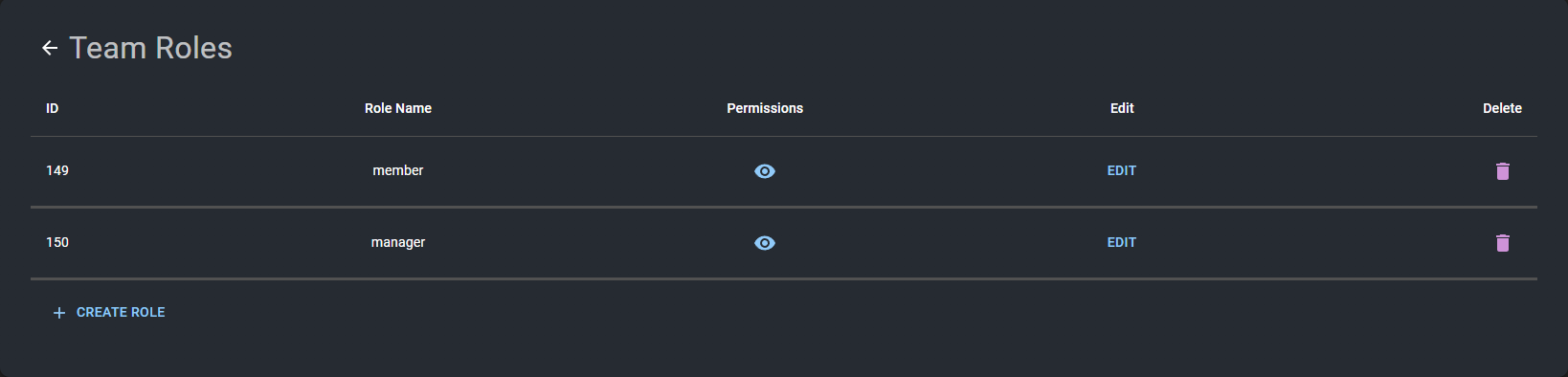
Team Roles
What Are Team Roles? #
Team roles in Vast.ai's platform are designed to streamline collaboration and enhance security by assigning specific permissions and access levels to different members of a team. These roles determine what actions a team member can perform and what data they can access within the team's shared workspace.
Types of Team Roles #
Predefined Roles: These are standard roles with preset permissions, suitable for common team structures. Examples include:
- Owner: Full access to all team resources, settings, and member management.
- Manager: Can access and work with team resources but is not the team owner.
- Member: Has ability to read and create instances, but no access to billing, team view, autoscaler, etc.
Custom Roles: Custom roles allow team administrators to create roles with tailored permissions. This feature is particularly useful for teams with unique workflow requirements or specific security protocols.
Creating Custom Roles #
- Accessing Role Management: Custom roles can be created and managed through the team's settings page on the Vast.ai platform.
- Defining Permissions: When creating a custom role, anyone with team_read and team_write access can select from a wide range of permissions, such as instance creation, billing access, monitoring, etc. This allows for precise control over what each role can and cannot do.
- Assigning Custom Roles: Once a custom role is created, it can be assigned to team members through the team management interface.
You can create roles either in the Vast CLI or on your team dashbaord if you have permission to create roles within your team.
You can easily edit any roles on your team using the team dashboard. When editing a role you should see a series of checkboxes and categories
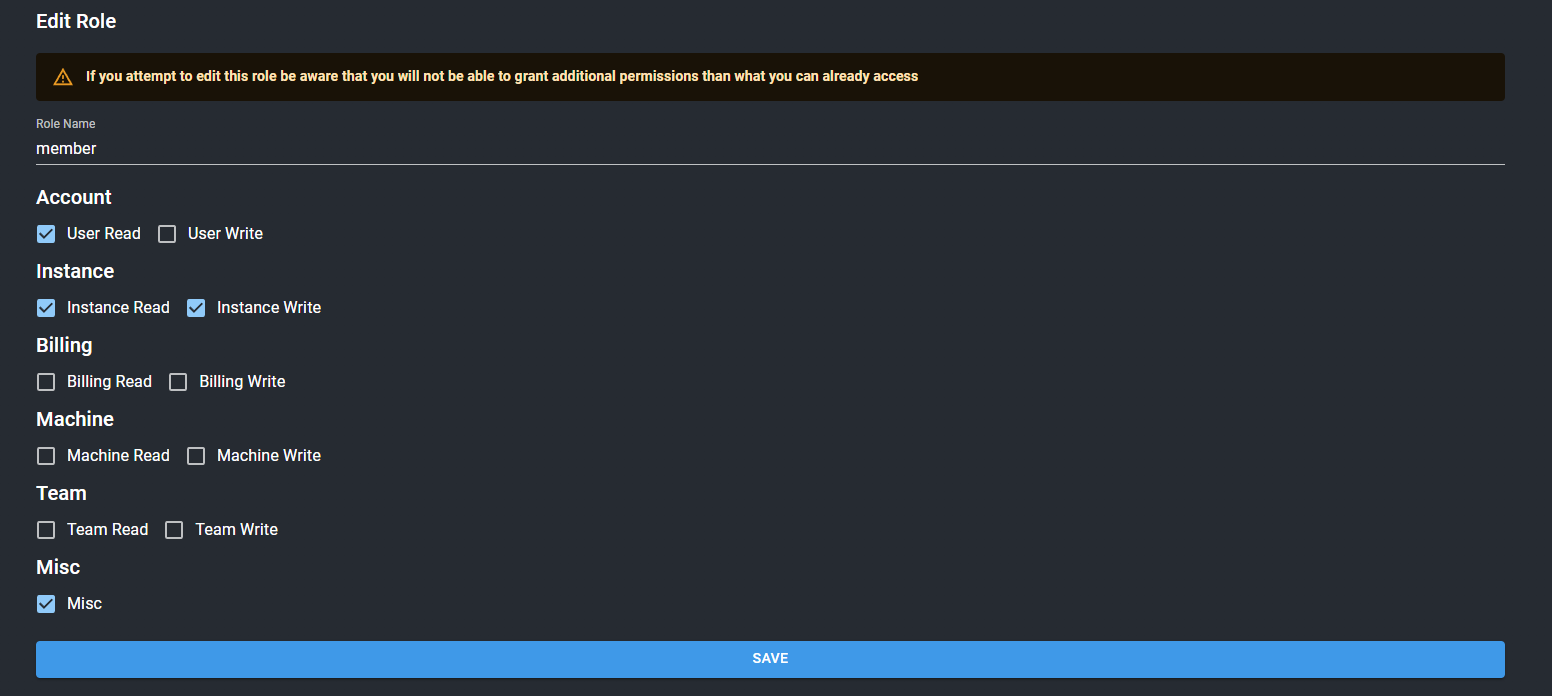
You can better understand what each checkbox represents by reading the role syntax below
Role Syntax #
All team roles are created through the team dashboard using the role editor. You can also create roles through the Vast CLI by passing in a permissions JSON object that delegates what group of endpoints can be accessed.
Currently, the system only supports groups of endpoint categories, but soon it will be extended for further granularity.
The current activated scopes are as follows
misc: Supports uncategorized operations like search offers, getting logs from various sources, etc
user_read: Allows the usage of obtaining basic user data like email, credits, etc. Essential for web usage.
user_write: Allows the ability to change account settings such as email, password, 2FA, etc.
instance_read: Grants ability to view instances, and certain read-only instance operations
instance_write: Grants access to instances and all relevant operations such as starting/stopping instances, cloud copy, reserving credits, etc
billing_read: Ability to view billing page and get billing information
billing_write: Ability to change billing page information
machine_read: Read access to machines owned by the team
machine_write: Ability to add/remove machines, and also edit machine settings
For teams usage you should create apikeys under the "api" section of permissions. An example of permissions json you would upload would be like this:
{
"api": {
"misc": {},
"user_read":{},
"instance_read": {},
"instance_write": {}
}
}This json would create a team role that would have miscellaneous access to things like search, be able to get basic information like your team's credits, team name etc, and also have the ability to create instances within the team context.
The main use case to use the json format to create a team role is the ability to enact granular permissions, for those trying to create a general team role it is better to create the role using the team dashboard.
In order to create a granular team role you must either use the CLI or the API
Best Practices for Using Team Roles #
- Clear Role Definitions: Clearly define the responsibilities and permissions for each role to avoid confusion and ensure effective collaboration.
- Use Custom Roles Judiciously: Create custom roles when predefined roles do not meet your specific needs. Be mindful of the permissions assigned to ensure team security and efficiency.
Team roles are a fundamental aspect of managing a collaborative and secure environment on the Vast.ai platform. By effectively utilizing predefined and custom roles, teams can ensure that each member has the appropriate level of access and control, fostering a productive and secure working environment.